Secure Communication through Quantum Physics
Overview Video – Learning Material – Exercises – Further Information & Literature – Quiz
If you are unsure about any terms, you can always check the glossary.
Overview Video
Learning Material
Communication is an important part of our daily lives. It has also played an important role in the history of mankind, especially secure, eavesdropping-proof communication. Classical cryptography offers interesting approaches to ensure this, but in principle classical approaches are not fundamentally secure. In addition, it is possible to intercept your communication without you noticing. Quantum physics offers fundamentally secure and tap-proof communication, especially a safe distribution of keys, which are used to encode encrypted messages. But how is this possible? And what is the underlying phenomenon?
Quantum physics provides two essential principles for ensuring secure communication: the No-Cloning Theorem and the Principle of Complementarity. The No-Cloning Theorem states that it is not possible to make an exact copy of the state of a single quantum object, meaning that it is not possible to make an exact copy which corresponds in every aspect to the original. The principle of complementarity is summarised in Basic Rule 4 as follows:
Basic Rule 4: Complementarity
There are pairs of observables that cannot be simultaneously prepared to certain values on an ensemble of quantum objects.
To illustrate the above, let us look at an example. Alice (person A) and Bob (person B) want to share a key via a secure channel. An eavesdropper, Eve, has access to their communication.
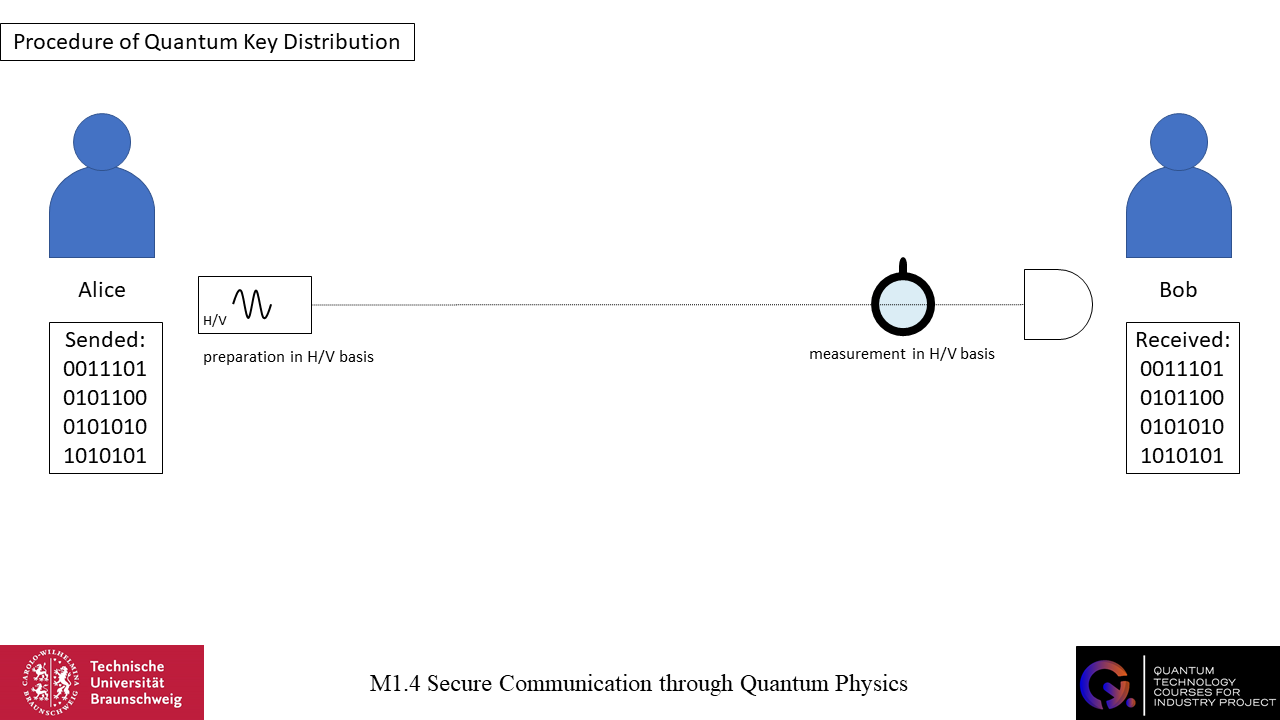
Key distribution takes place via the polarisation state of individual photons. There are two bases with a total of four polarisation states. One is the H/V basis with horizontally and vertically polarised photons, and the other is the +/- basis with +45° and -45° polarised photons. Alice and Bob will encode an H or +45° photon with a 1 and a V or -45° photon with a 0. This way they will be able to send bit sequences. To ensure key distribution, Alice and Bob must work within the same base. Alice is the transmitter and Bob is the receiver. As the sender, Alice prepares a single photon in a particular state, for example a horizontally polarised photon. She anounces this Bob and sends the prepared photon. Bob then measures the photon in the H/V basis and measures H (the detector detects the photon), which is coded as 1. This is how Alice and Bob can communicate. Alice sends prepared photons of a particular polarisation, anounces this Bob and Bob receives these photons, measures them on the correct basis and receives the polarisation chosen by Alice. Either the photon is going to be detected – the photon is not absorbed by the polarisation filter – or the photon is not going to be detected – the photon is absorbed by the polarisation filter.
Now we consider a third person, Eve. Eve has access to the communication between Alice and Bob. To get the information that is being communicated, Eve has to measure the state of the photon, because it is not possible to copy quantum objects (the no-cloning theorem). So unlike classical eavesdropping, where you might be able to copy the message and remain unnoticed, you cannot do this in quantum eavesdropping. All in all, Eve has to measure the state of the photon, and to do this she has to measure it in a particular basis.
We assume that Alice and Bob are working in the same base, so if Alice prepares the photon in H/V base, Bob measures it in H/V base, and if Alice prepares the photon in +/- base, Bob measures it in +/- base. For now, it is not important how Alice and Bob know which base they are working in.
In this context, there are two possible outcomes. Either Eve works in the same base as Alice and Bob, or Eve works in a different base to Alice and Bob. We will look at both scenarios.
If Eve is working in the same base as Alice and Bob, she can measure the state of the photon. Afterwards she can prepare a photon with the same state and send it to Bob. The eavesdropping will go unnoticed.
If Eve is not working in the same base as Alice and Bob, she will not be able to obtain information about the initial state of the photon due to complementarity. Instead, she will measure a random state of the other base. She sends a photon to Bob, which is prepared in a different basis. Bob measures the photon and gets a random result that may differ from Alice’s initial result. But why does this happen?
At the beginning, the photon has no definite state. Alice prepares the photon and gives the photon a certain state, for example she prepares a photon that is horizontally polarised. A measurement in H/V basis would now give a clear and definite result that the photon is horizontally polarised. Now, the principle of complementarity states that there are pairs of observables that cannot be simultaneously prepared to certain values. The polarisation in H/V basis and +/- basis are observables and additionally complementary observables. If you perform a measurement in +/- basis, you perform a measurement on the photon in a basis that is complementary to its basis of preparation. The photon is prepared in H/V basis, but is measured in +/- basis; H/V and +/- basis are complementary observables. Because of the fact that the photon is already prepared in H/V basis, it cannot simultaneously be prepared to a certain value in +/- basis. Therefor, the measurement in +/- basis will give random results. As a consequence, Eve does not receive any useful information about the bit sent by Alice. Also, it is not possible to derive the previous state from the measured value, the measurement in the complementary basis provides truly random results. An analogy to complementarity is given by the image which shows two intertwined circles. If you remove one of the circles, the other circle is incomplete. It is not possible to remove the other one as a whole circle, some parts are missing.
We will look at different scenarios to get a deeper insight and to work out different processes. Again, Alice and Bob want to communicate via the polarisation state of single photons, and Eve is an eavesdropper and has access to their communication. Alice and Bob always work in the same base. We do not go into further details, such as how they manage to work in the same base, or how Alice knows that Bob has the same base.
In the first scenario, Alice and Bob do not change the base. So they always work in either the H/V base or the +/- base. Eve knows that they do not change the base and also works in one base. There is a 50% chance that Eve will choose the right base. If she chooses the right base, the eveasdropping will go unnoticed. If she chooses the wrong base, there is a 50% chance that she will get a random result that matches the original message. She then sends photons to Bob, but Bob will measure them in the wrong base (with respect to Eve’s base) and will also get random results. In this context, Bob’s results will differ from Alice’s with a probability of 50%, so we conclude that nearly 50% of the messages received by Bob will be wrong. When Alice and Bob compare the values, they will notice the eavesdropper Eve.
In the second scenario, Alice and Bob randomly change their bases after each bit of information. So they can stay in the same base or change base after one bit of information. Now it makes no difference whether Eve knows whether Alice and Bob change bases or stay in one base all the time. Eve’s base will randomly coincide with Alice and Bob’s base. The probability is 50%. If Eve has the right base, Alice and Bob will not notice anything. If Eve has the wrong base, there is a 50% chance that Alice and Bob will notice the eavesdropping. Since the base changes randomly after each bit, the whole message is likely to be wrong 25% of the time and the eavesdropping will be noticed.
All in all, we can conclude that the principle of complementarity and the no-cloning theorem are fundamental to secure the distribution of keys. In theory, it is possible to ensure secure communication based on quantum physics. However, the application of the theory can be difficult…
Exercises
Exercise 1:
Name the Basic Rule 4 and explain its meaning.
Exercise 2:
Using the example of Alice, Bob and Eve, briefly explain why quantum key distribution is theoretically secure.
Exercise 3:
The image shows an experimental setup which consists of three polarisation filters, a single photon emitter and a detector. Describe the different scenarios that can occur and explain why the probability of detecting a photon is 12.5%.
Exercise 4:
Work out two possible scenarios in which another eavesdropper, Evelyn, is placed between Eve and Bob, but is not aware of Eve’s existence. Is there a chance that Bob will get the correct bit information even though Eve used a different base to Alice and Bob? And what does this mean for the success of Evelyn’s eavesdropping?
Solutions:
Further Information & Literature
BB84 Protocoll:
Bennett, C.H. & Brassard, G. (1984). Quantum Cryptography: Public Key Distribution And Coin Tossing. International Conference on Computers, Systems & Signal Processing, December 10-12. Bangalore India. pp. 175-179.
Mullins, J. (2002). Making Unbreakable Code: The quantum properties of photons could make encrypted messages absolutely secure. IEEE Spectrum. pp. 40-45.
Müller, R. & Greinert, F. (2024). Quantum Technologies: For Engineers. De Gruyter.
Scully, M.O., Englert, B.-G. & Walther, H. (1991). Quantum optical tests of complementarity. Nature, Vol. 351. pp. 111-116.
