The E91-Protocol
The E91 protocol represents a major advance in quantum key distribution (QKD) because it relies on quantum entanglement to generate a secure key. It was named after its developer Artur Eckert and the year 1991. Entanglement is one of the most fascinating phenomena in quantum physics and is fundamental to the security of the E91 protocol. One can picture this with two dice that always show the same number, no matter how far apart they are. This synchronized behaviour is due to the fact that entangled particles share a common quantum state that cannot be decomposed into independent individual states. A measurement on one particle therefore simultaneously fixes the outcome for the other—regardless of their spatial separation.
In the E91 protocol, Alice and Bob use pairs of entangled quantum objects—entangled photons, for example—to generate the encryption key. A central source sends entangled quantum objects to Alice and Bob, who then perform measurements independently. Because of the entanglement, the measurement results are correlated, enabling both parties to generate matching keys.
Basic setup
The E91 protocol deals with the exchange of an encryption key between two communication partners. For the sake of illustration we consider two people: Alice (person A) and Bob (person B). The meaning and function of an encryption key have already been explained in Chapter 1.
Appropriate technical devices are required for QKD to take place successfully. In what follows you can explore interactively the operation and structure of the components used in the E91 protocol:
Videos are used to explain the key distribution process step by step. First, a simple key exchange between Alice and Bob is demonstrated, and then a variant is presented in which an eavesdropping attempt by the eavesdropper Eve is simulated:
Polarization describes the direction of the oscillation of a wave. One distinguishes between the H/V basis and the +/- basis. In the E91 protocol the polarization directions of 22.5° and 67.5° are also considered, because only by including them is it possible to check for possible eavesdropping attacks. These additional polarizations represent different tilt angles of the wave.
Entanglement is a central phenomenon of quantum physics: two or more quantum objects can form a joint state that cannot be written as a product of individual states. A measurement on one of the quantum objects projects the joint quantum state; if one then performs the same measurement on the other quantum object, its outcome is already fixed—independent of the spatial separation of the entangled quantum objects. Experimentally, this basic principle is manifested as correlations or anticorrelations.
Entanglement is a powerful tool that the E91 protocol uses to guarantee security and to detect possible eavesdropping. Entangled quantum objects are treated as a single overall system—any change to one object affects the other instantly, regardless of distance. Experimentally this interaction manifests itself as correlated or anticorrelated measurement results. Within the scope of the protocol, the module and the course we assume that the measurement results are anticorrelated.
We now return to the communication scenario between Alice and Bob. In reality neither party knows which polarization basis the other has chosen—this was a simplification up to now. How does the communication proceed in that case?
Entanglement means that the photons measured by Alice and Bob form a single overall system. After both photons are measured the results are anticorrelated—even when the photons are far apart.
Let us now introduce a third party, Eve, the eavesdropper. Eve intends to intercept the encryption key and thus gain access to the communication between Alice and Bob. We assume that Eve can access both the quantum channel and the classical channel.
The no-cloning theorem, introduced in Chapter 1, states that it is impossible to create an exact copy of an unknown quantum state.
A distinctive feature of the E91 protocol is that an eavesdropping attack can be detected because of the nature of entangled particles. Eve’s intervention disturbs the entanglement: it is comparable to trying to tamper with one of the “magic cards” in the card analogy—the perfect synchrony between the cards is lost, so Alice and Bob register unexpected measurement results. The E91 protocol therefore contains an integrated security mechanism: any interference disrupts the quantum connection and produces detectable errors. If the error rate exceeds a certain threshold, Alice and Bob can determine that the key has been compromised and can terminate the communication in order to preserve the confidentiality of sensitive data.
The security of the E91 protocol is based on fundamental physical laws and thus remains largely inviolable even in the face of technological advances.
Nevertheless, the protocol does have vulnerabilities. For example, an attacker could try to manipulate the source of the entangled photons in order to interfere with the communication without being detected.
In addition, the E91 protocol is relatively complex, because checking for an eavesdropping attack involves testing Bell’s inequality—this requires three polarization bases, whereas the BB84 protocol needs only two.
One year after E91 a simplified protocol was proposed: it adapts the BB84 scheme to entangled photons. The BBM92 protocol, named after its inventors Bennett, Brassard and Mermin (BBM) and the year 1992, works with only two polarization bases.
Whereas in Chapter 1 information was exchanged from a sender (Alice) to a receiver (Bob), the present chapter employs the principle of entanglement to guarantee security: both communication partners have to measure the state of the quantum object actively.
Quantum entanglement is a central phenomenon of quantum physics: it links the state of one qubit to that of another—regardless of the distance between them. This property creates an ultra-secure connection in which a change to one qubit has immediate consequences for its entangled partner.
That makes entanglement a powerful tool for advanced quantum-communication protocols and opens up further applications such as quantum teleportation, in which a quantum state is transferred between distant locations.
Quantum teleportation is not part of the E91 or BBM92 protocols but is closely related to entanglement. For that reason an introduction to quantum teleportation follows here.
Assume that Alice and Bob share an entangled photon pair. Alice holds one photon, Bob the other; neither photon has yet been measured.
Quantum teleportation forms the basis for building quantum networks over large distances. It enables the transfer of quantum information without a direct physical transmission channel, thereby acting against loss and decoherence. By means of teleportation distant network nodes can be interconnected, the integrity of quantum states can be preserved, and the development of a global quantum internet can be advanced. Robust and efficient communication channels are essential to guarantee the secure and loss-free worldwide transmission of information.
Exercises:
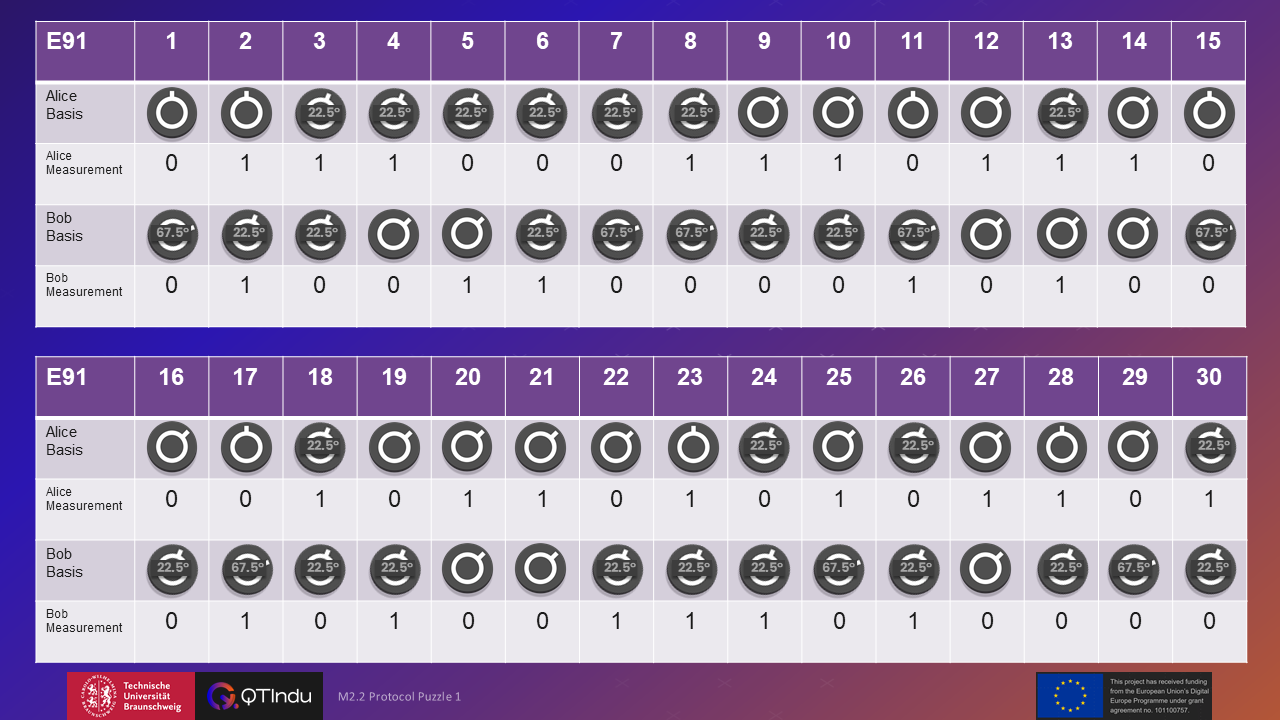
Exercise:
The illustration shows an excerpt of the communication between Alice and Bob. Analyse whether an eavesdropping attack has taken place. If not, specify the key that can be extracted from the illustration.
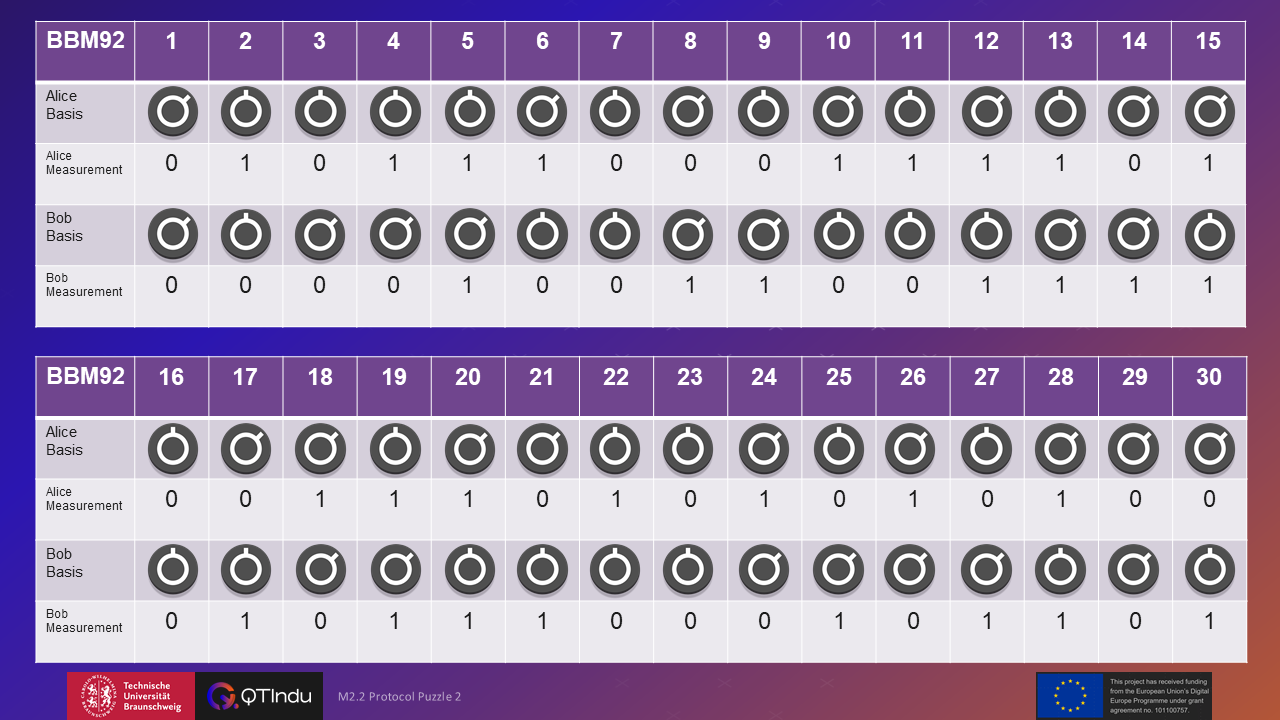
Exercise:
The illustration shows an excerpt of the communication between Alice and Bob. Analyse whether an eavesdropping attack has taken place. If not, specify the key that can be extracted from the illustration.