The BB84-Protocol
The BB84 protocol is the cornerstone of Quantum Key Distribution (QKD) and was the first method to use the principles of quantum physics to exchange secure keys. It is named after its inventors, Charles Bennett and Gilles Brassard, and the year of its development (1984). This well-known QKD protocol exploits the polarization properties of photons to generate and exchange an encryption key securely between two parties. In doing so it prevents an eavesdropper from intercepting the key without being detected.
Basic terminology – from bits and qubits to photons and quantum objects
Particles, waves and quantum objects
At the outset it is useful to clarify some central concepts. In classical physics a distinction is made between particles—discrete, located at a specific place at a specific time, with mass, spatial extent, and so on—and waves—continuous, present at several places at the same time, capable of interference, and so forth. Quantum physics, however, has shown that this classical distinction cannot be maintained at the smallest scales: particles display wave-like properties and waves can behave like particles.
To do justice to this phenomenon, the term quantum objects is often used in quantum physics. Such objects exhibit both wave-like and particle-like characteristics and show phenomena that occur only in the quantum-mechanical realm.
Photons as important quantum objects
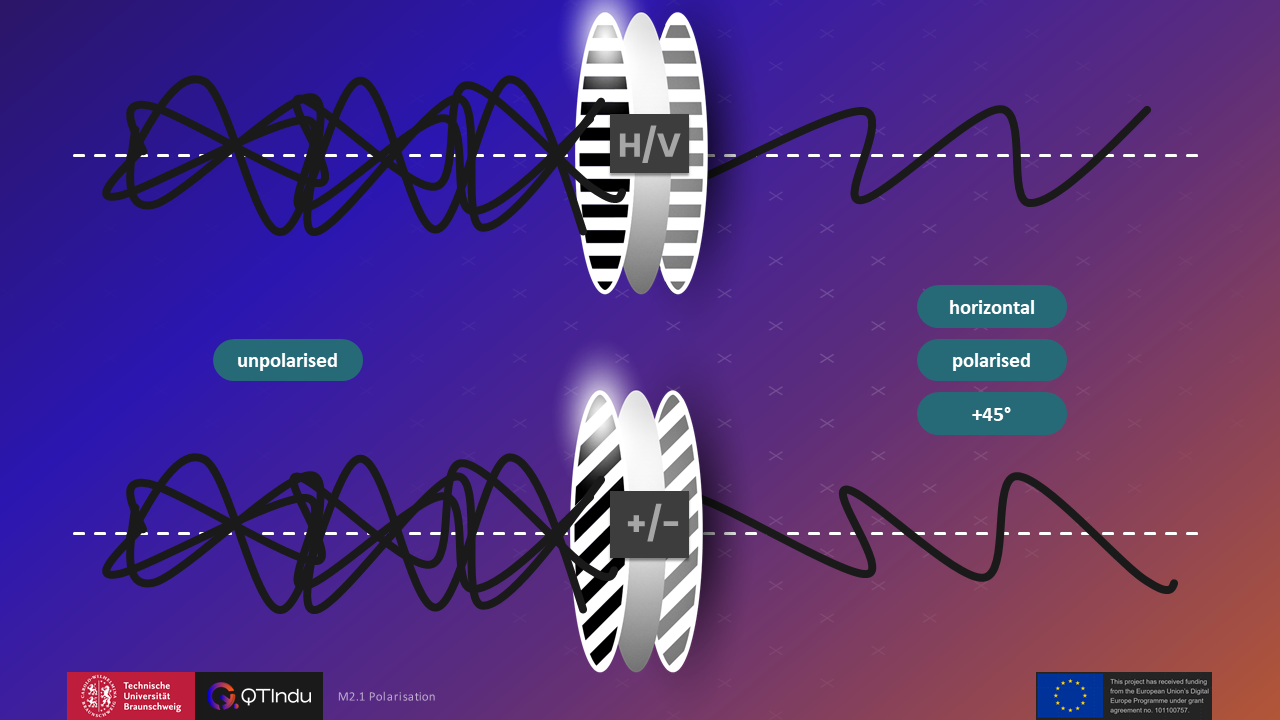
One important quantum object is the photon, the smallest packet of light energy. In QKD, photons serve as information carriers. Classical light can be described as a stream of photons that—similarly to classical light waves—can possess a certain polarization. Polarization is the direction of the wave’s oscillation. Photons can be linearly polarized by means of polarization filters. Most everyday light sources are unpolarized because they contain a mixture of differently polarized light. Quantum-communication systems preferably employ single photons because they take on the role of quantum bits (qubits) there.
Bits and qubits
In computer science the classical bit is familiar; it can take the values 0 or 1 and is the fundamental unit of any digital information. When classical bits are transmitted an electrical signal is often used: a low or zero voltage represents the binary value 0, a high voltage the binary value 1.
A quantum bit (qubit) is the counterpart of the bit in the quantum world. A qubit can likewise assume the binary values 0 or 1, but it is subject to the laws of quantum physics. As a result it possesses additional features such as superposition, entanglement, and other quantum-specific properties. Before measurement a qubit can be in a superposition state and hold the binary values 0 and 1 simultaneously. Only through measurement does the qubit adopt a definite binary value (0 or 1), which, however, is obtained randomly and probabilistically.
Quantum states, coherence and decoherence
A quantum state describes the properties or configuration of a quantum object or system. In the classical world a state can be measured unambiguously without the act of measurement changing that state itself. In quantum physics the behaviour of a qubit in a superposition state does not conform to this notion: only measurement forces the system into a definite (classical) state.
Coherence time is the period during which a quantum object maintains its quantum state with all its quantum-specific features (e.g., superposition, interference, entanglement). The system remains stable in its quantum state until external influences lead to decoherence. Decoherence is the loss of quantum-specific properties through interactions with the environment and presents a particular challenge for quantum communication and quantum computing. A coherence time that is as long as possible is crucial for ensuring reliable and stable quantum communication.
The basic structure of quantum communication
Protocols in quantum communication, and especially in QKD, aim to exchange a secret encryption key securely between two parties—often called Alice (A) and Bob (B). The encryption key is a one-time pad. This key is at least as long as the message to be protected and is generated anew for every message. When applied correctly, the one-time pad is provably secure and cannot be broken even with unlimited computational resources. Once Alice and Bob have obtained a key in this way, Alice can encrypt her message and send it to Bob, who decrypts it with the same key. The protocols themselves describe only the secure key exchange, not the actual encryption and decryption of the message.
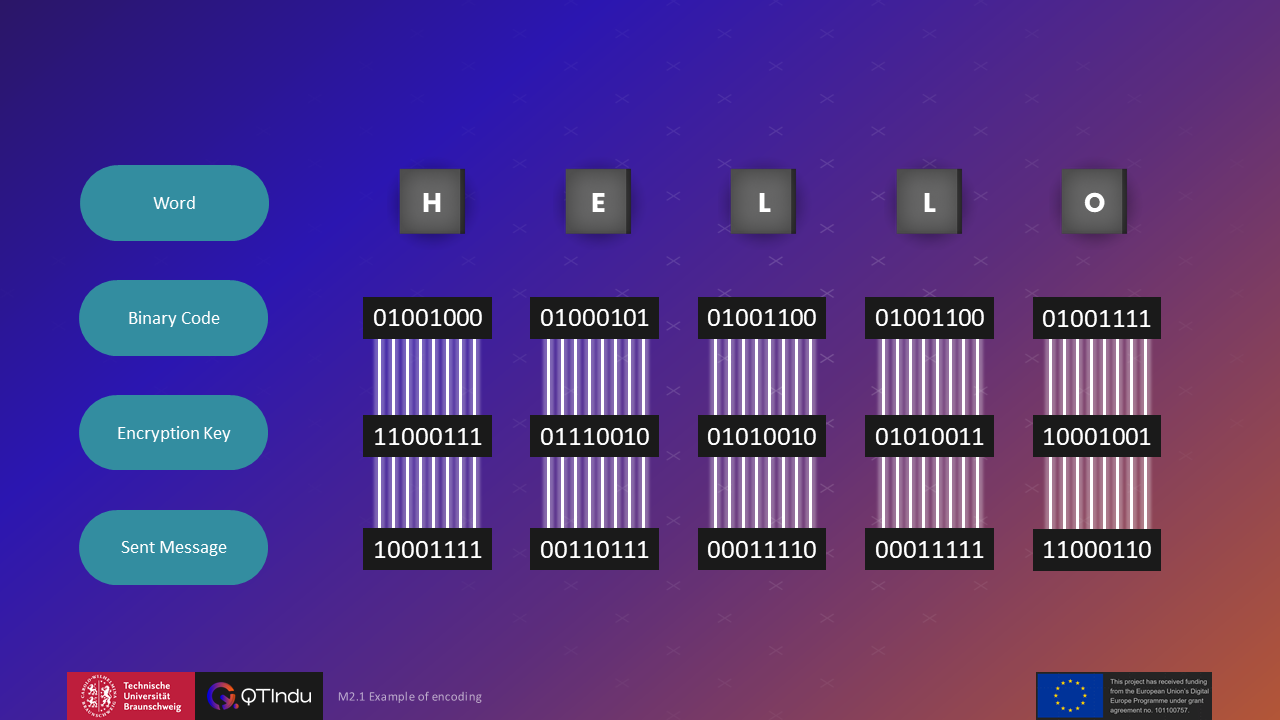
Example of a simple encryption
Any information—letters or numbers—can be represented as a sequence of binary values. The ASCII binary representation of the word “HELLO” is, for example:
01001000 01000101 01001100 01001100 01001111
Using QKD, Alice and Bob have shared a common encryption key, which in this example could be:
11000111 01110010 01010010 01010011 10001001
To encrypt the message, each bit in the resulting binary sequence remains the same when the corresponding key bit is “0” and is inverted when the key bit is “1”.
Bob decrypts the received, encrypted message in the same way: he compares it with the same key and again inverts every bit for which the key is “1”. This allows him to reconstruct the original message.
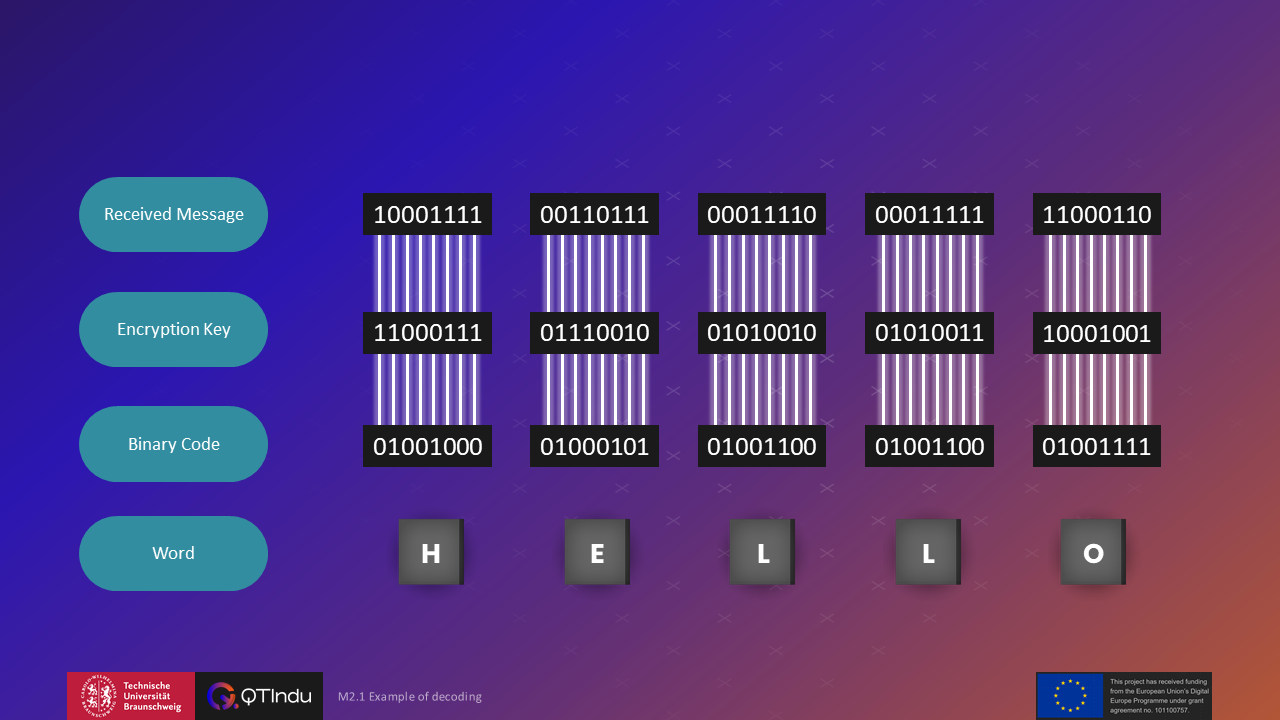
This consideration shows how essential a cryptographically strong and securely distributed key is for the effective protection of a message. The BB84 protocol and other QKD methods are devoted precisely to this purpose: they ensure that Alice and Bob can generate a key that cannot be read by unauthorized parties without revealing their presence.
For the BB84 protocol to be carried out successfully, Alice and Bob require various devices. The following provides an overview of the basic setup and the most important components:
Step by step: procedure of a quantum key distribution
The following describes a simple key exchange between Alice and Bob. Afterwards we show how this procedure changes when the eavesdropper Eve attempts an attack.
Polarization denotes the direction of the wave’s oscillation. In this module two bases are considered: H/V and +/-, i.e. horizontal/vertical and 45°/135°.
Preparation is a procedure in which a quantum object (e.g., a photon) is put into a desired state. If a photon is prepared as “horizontally polarised”, it will pass all filters that transmit horizontally polarised photons. It is important to note that preparation is different from measurement. If a photon is reflected at a beam splitter, this does not automatically mean it will always be reflected—this is not preparation but merely a measurement of that single interaction.
In the “simple” example described here Bob knows the polarization basis chosen by Alice. In practice (and in the actual BB84 protocol) this is not the case. Bob must choose a basis randomly, which is at the heart of the protocol’s security.
With this overview of the required devices, the setup, and the first steps in key exchange you have a foundation for understanding the further course of quantum key distribution and potential eavesdropping attacks.
In the next video, we consider the case in which Alice and Bob do not know which polarization basis the other has chosen during key distribution:
When Alice and Bob use different bases, they discard the corresponding bit values. But why must the polarization bases match? Why are values obtained with different bases discarded?
Superposition is an important phenomenon. In the context of quantum physics and quantum technologies, it denotes the coexistence of several classical states and thus the probability distribution of possible measurement outcomes. Only a measurement fixes the photon to a definite, measurable value. A quantum bit (qubit) can be in a superposition of different classical states (0 and 1). This distinguishes it from classical bits and enables complex and secure transmission methods.
Complementarity is a multi-faceted concept. Here only one aspect is considered. H/V and +/- are complementary observables. If a photon is prepared unambiguously in one basis, a measurement in the other basis produces random results. Such results are worthless because they do not correspond to the prepared value, but are merely random. For this reason, Alice and Bob discard all values for which their polarization bases do not match.
In practice Alice and Bob encounter another obstacle: Eve, the eavesdropper. She tries to tap the communication between Alice and Bob. How QKD protects itself against eavesdropping is explained in the following sections:
In quantum physics it is impossible to copy a quantum state exactly. This property is often compared to trying to duplicate a unique painting perfectly—every attempt fails or changes the original. Consequently, Eve cannot create unnoticed backups of quantum states; every measurement necessarily affects the photons and can thus be detected.
Within the BB84 protocol an error rate of 25 % plays a key role in detecting an eavesdropping attack. Because Alice and Bob choose their polarization bases randomly, their choices differ in half of the cases (50 %) when Eve tries to read the photons. If Eve measures in the wrong basis in these cases, she also prepares the photon for Bob in the wrong basis. Complementarity then causes Bob to obtain an incorrect result in 50 % of those instances. Thus, 50 % of 50 % of the cases lead to an error. The error probability is therefore 25 %, affecting a significant portion of the transmitted bits and indicating suspicious interference.
Summary and advantages of the BB84 protocol
Detection of eavesdropping
Any attempt to eavesdrop changes the quantum state. If too many discrepancies are found in the subsequent bit comparison, Alice and Bob detect an attack and discard the compromised key.
No direct transmission of the key
Alice and Bob never transmit the complete key itself; they share only information about the measurement bases. The key therefore remains secret at all times.
Physical security instead of computational complexity
Unlike classical methods that rely on hard mathematical problems and could be broken by greater computing power, BB84 relies on fundamental laws of quantum physics.
Future-proof solution
Because BB84 does not depend on computation-based security models, it remains robust even against future threats such as quantum computers.
The last video has illustrated the original BB84 protocol. By combining random basis choices, the no-cloning theorem, and the subsequent comparison of their measurements, BB84 provides a mechanism for generating a secure key and unambiguously identifying any eavesdropper.
Exercises:
Exercise:
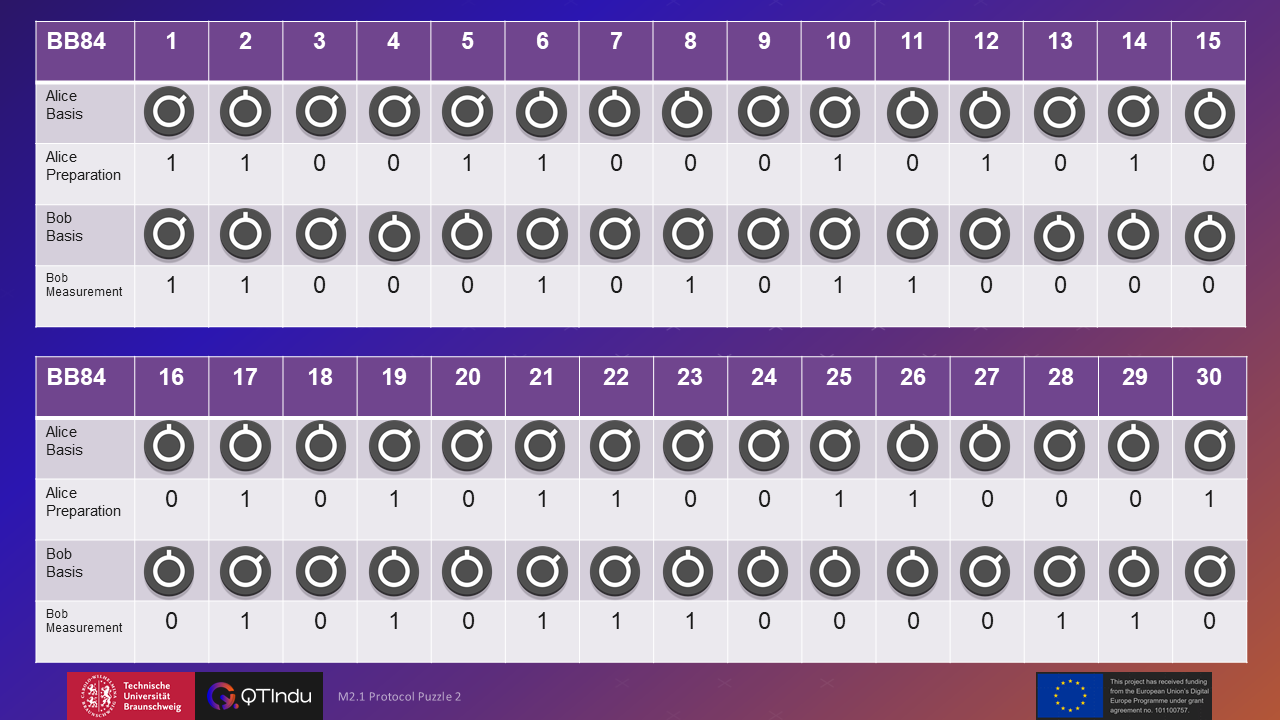
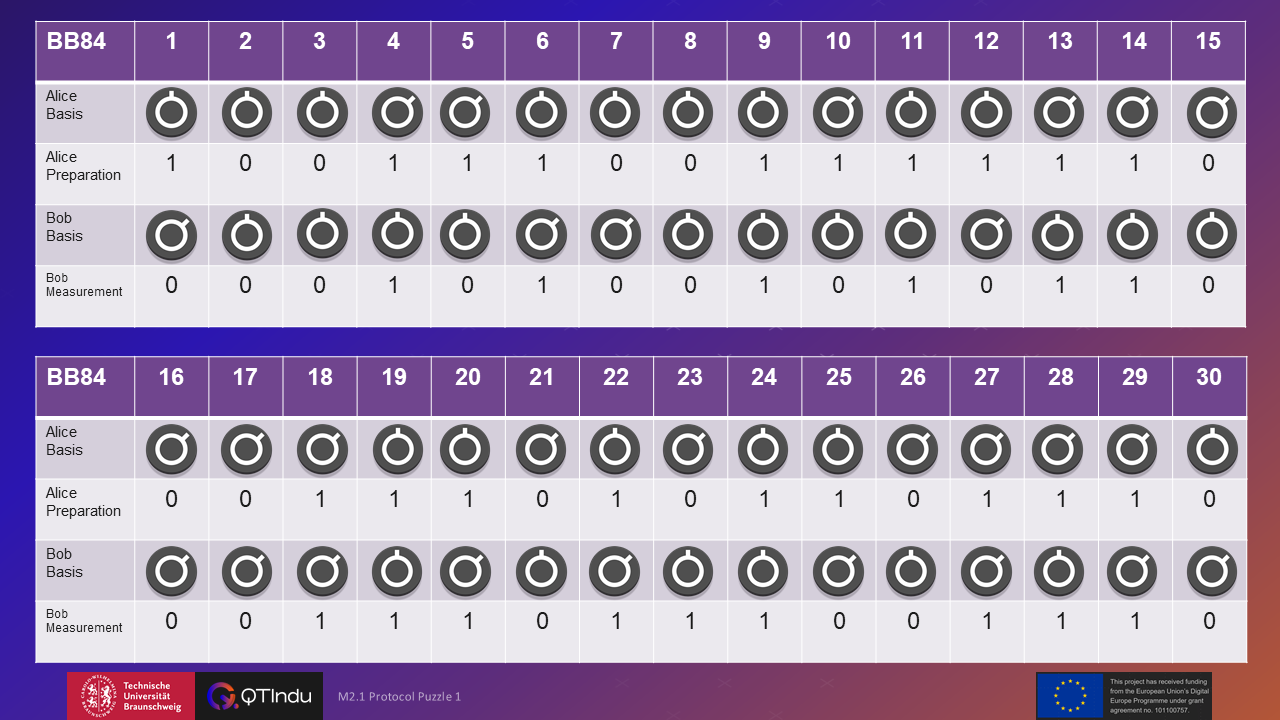
The illustration shows an excerpt of the communication between Alice and Bob. Analyse whether an eavesdropping attack has taken place. If not, specify the key that can be extracted from the illustration.
Exercise:
The illustration shows an excerpt of the communication between Alice and Bob. Analyse whether an eavesdropping attack has taken place. If not, specify the key that can be extracted from the illustration.